The first question is: what for? There are a lot of reason for example someone download Windows application from Linux Apache server. The downloaded application is signed in runtime with different certificate according to selected license. Later during execution Windows application checks certificate type, revocation status and blocks or grants some features. Also application may use OCSP to obtain certificate status.
Below is an example how to sign Windows application on CentOS7 VM.
For signing I choose my application usb-cubby.exe which I developed to save my Internet credentials in encrypted way.
Currently application properties does not show Digital Signatures tab:

Now from CentOS7. Download usb-cubby.exe:
|
# curl -O http://data-cubby.ladydebug.com/usb-cubby.exe |
Creating self-signed certificate:
|
# openssl req -x509 -nodes -days 365 -newkey rsa:2048 -keyout private.key -out selfsigned.crt Can’t load /root/.rnd into RNG 139879911084480:error:2406F079:random number generator:RAND_load_file:Cannot open file:../crypto/rand/randfile.c:88:Filename=/root/.rnd Generating a RSA private key ..+++++ ………………….+++++ writing new private key to ‘private.key’ —– You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter ‘.’, the field will be left blank. —– Country Name (2 letter code) [AU]:CA State or Province Name (full name) [Some-State]:Ontatio Locality Name (eg, city) []:Ottawa Organization Name (eg, company) [Internet Widgits Pty Ltd]:CentOS7 Organizational Unit Name (eg, section) []:Software Common Name (e.g. server FQDN or YOUR name) []:ladydebug.com Email Address []:alex@ladydebug.com |
Installing osslsigncode:
|
# wget https://downloads.sourceforge.net/project/osslsigncode/osslsigncode/osslsigncode-1.7.1.tar.gz # tar -xvf osslsigncode-1.7.1.tar.gz # sudo yum install libgsf.x86_64 # sudo yum install autoconf # cd .. |
Signing usb-cubby.exe with created self-signed certificate:
|
# osslsigncode sign -certs ./selfsigned.crt -key ./private.key \ > -n “USB Cubby” -i http://data-cubby.ladydebug.com/ \ > -t http://timestamp.digicert.com \ > -in ./usb-cubby.exe -out ./usb-cubby-signed.exe Succeeded |
Verifying result, the size of signed file is bigger the the size of not-signed version:
|
# ls -l usb-cubby* -rw-r–r–. 1 root root 77824 Jan 24 18:32 usb-cubby.exe -rw-r–r–. 1 root root 82800 Jan 25 10:21 usb-cubby-signed.exe |
From Windows PC. Using pscp.exe utility from PUTTY package transfer usb-cubby-signed.exe to the Windows machine:
|
>”c:\Program Files\PuTTY\pscp.exe” -P 22 root@192.168.2.118:/Alex/usb-cubby-signed.exe usb-cubby-signed.exe |
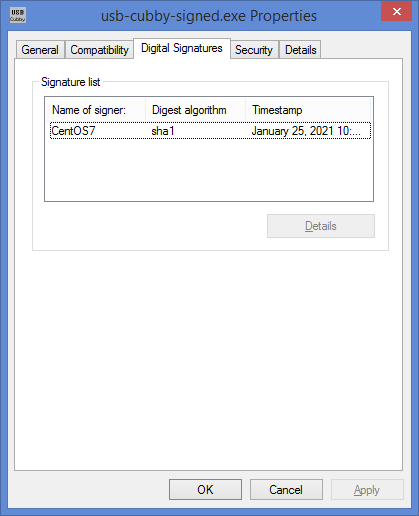
Digital signatures of usb-cubby-signed.exe:
A bit more:
Creating pfx file from crt and private key file:
|
# openssl pkcs12 -export -out selfsigned.pfx -inkey private.key -in selfsigned.crt Enter Export Password: Verifying – Enter Export Password: |
Extractiong public key from selfsigned.crt file:
|
# openssl x509 -in selfsigned.crt -pubkey -noout > pubkey.pem |